Content Contributor, E-N Computers
7+ years experience in healthcare IT and tech support.
Some of our new clients already have an in-house IT department that they want to supplement. Usually, this is because they’re stretched thin or need specialized professionals for certain projects and problems. We’re proud to partner with organizations like these by providing co-managed IT services.
Supplementing your internal IT with co-managed IT services provides several benefits. Our Tier 2 help desk are an experienced backup when your on-site staff need assistance resolving complicated issues. Our knowledgeable network administrators maintain high performance and security across your network, freeing up time to focus on more business-specific projects. And our consultants will help you develop a comprehensive IT strategy and budget that fits the realities of your business. All of these are solid wins for your organization.
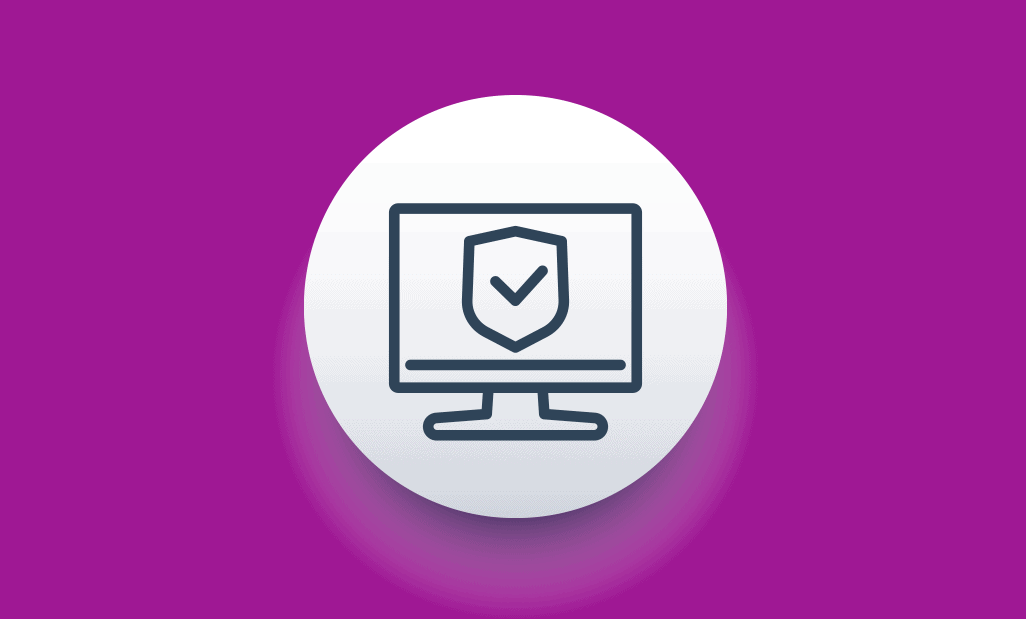
To achieve these benefits, cooperation between your internal team and our team is essential. We will work together to address the questions and challenges that arise during an IT transition. These questions revolve around 1) system security, 2) continuity of service, and 3) processes and procedures.
Let’s look at how to achieve the first key to a successful IT transition: system security.
QUICK ANSWER:
How can we achieve a successful IT transition?
Use your time wisely. Make sure your organization has full control of IT accounts, a clear plan for continuing to provide service, and complete documentation of key systems and data – including maintenance and backup processes.
System Security
Document and properly configure all background services. Too often, we see background services that use the account of an IT person or a default IT administrator account. When these accounts are disabled, the services stop working. Scheduled jobs like backups and network scans are commonly disrupted as a result.
You can avoid such service disruptions by properly configuring and documenting these services. List out each service, what it does, and what account credentials it uses. It is preferred that services run using special service accounts that do not allow interactive logon.
Eliminate any default or shared IT administrator passwords. Sharing accounts and passwords, including using a default or generic administrator account, is terrible security practice. At minimum, the password would need to be changed every time a person who knows the password leaves, so that they no longer have access. But even if no one is leaving, sharing passwords is a bad idea. It makes it much harder, if not impossible, to use computer logs to identify the person responsible for a system change.
As part of your IT transition, discontinue the use of shared accounts and passwords. This is often done in tandem with changing background services to use their own non-interactive accounts. As a result, your services will remain online, your departing users will not have a way to continue accessing your systems, and you will be better able to make use of logs when investigating a problem.
Send multi-factor authentication codes to a company-controlled device or account. Multi-factor authentication is useful for all employees but especially for those with additional permissions, such as IT staff. Depending on the service being accessed, verification codes may be retrieved from email, SMS, or an authenticator app.
During a transition, make sure that any accounts with MFA are configured to send codes to a company-controlled email, phone number, or authenticator app. This will help ensure you maintain access to critical systems and information.
Continuity of Service

Submitting support requests. With internal IT, you’re used to a quick walk by the IT office or mentioning an issue when passing them in the hallway. This way of reporting issues is largely ineffective with co-managed IT. It leads to issues being forgotten and unresolved. The solution is to build a culture of submitting tickets.
Submitting tickets, or requests for help, ensures there is a record of the request that can be reviewed and added to by both your internal IT person and the team co-managing your technology. Tasks can be assigned to a technician and escalated to someone more experienced when needed. Line managers and users can check the status of their tickets using a web portal. Tickets enable us to properly prioritize work, maintain accountability, and offer transparency. They allow the internal team and the managed services provider to work together more effectively.
Implementing service levels. Service levels are an important tool for ensuring that problems are prioritized correctly. We prioritize tasks based on how many people they affect and their impact on business operations. You can see our service levels and response time goals in this article, which discusses some perceived disadvantages of managed IT services. As mentioned there:
While some problems may not be handled as quickly as you have become accustomed to, our triage process ensures that every problem is handled in a timely manner. It enables us to identify trends and deal with underlying issues before they become more serious. And it allows us to provide quality support your entire team needs at a reasonable price.
Pending tasks and projects. One reason companies move to co-managed IT is because their internal department is overworked. Despite efforts to prioritize, urgent tasks are resolved before important ones, creating a backlog of tasks needing attention. One company that partnered with us had 350 unresolved tickets! And a ticket queue may not tell the whole story.
In organizations where users are not trained to submit tickets, or where the IT department does not keep such records, it can be difficult to identify all the issues needing attention. During a transition, it is important to document all these incomplete tasks and projects for future planning.
Helpdesk availability, on-site support, and other services. When we provide fully managed IT services, your staff can contact our helpdesk by phone, chat, or email for all issues. On the other hand, our co-managed IT plan provides Tier 2 helpdesk support for issues that your on-site technician is unable to resolve. Our helpdesk keeps regular business hours, so most after-hours calls and emails will be processed the following business day. However, after-hours emergency service is available.
In addition to remote support, we provide on-site support during regularly scheduled visits. This helps us to build a good relationship with your staff and have a better pulse on the overall condition of your technology infrastructure. Our visits are coordinated with your staff contact so that they are as beneficial as possible.
Because we primarily provide remote support, we don’t usually do equipment set-up for events like board meetings and conferences. If this is something you need, please discuss it with us early on. We also make a clearer separation between IT and IT-adjacent tasks; for example, although checking security camera footage is technology-dependent we do not perform this service. We may be able to help you retrieve a portion of footage and transfer it to a flash drive, however.
One of our goals during an IT transition is to reset expectations within your company of how IT operates. Our operating model is designed to provide high quality support to your entire organization, with accountability and transparency baked in. With support from your company leadership, we can help all staff adjust to changes like ticket submission, helpdesk availability, and service levels.
In addition to introducing our standard operating procedure to your organization, we will work to learn and document your processes. What does that look like?
Processes and Procedures
Your IT runbook outlines critical details about your systems. It includes information about system configuration, security controls, maintenance, and back-ups. It also describes how to stop, restart, and recover critical servers and applications. Having this information written down makes it more likely that all steps are followed consistently. It is also an excellent resource for training new IT staff. Your team will always have the latest version of this document because it contributes to the success of your organization.
Organizational Success

When IT staff aren’t constantly putting out fires or doing routine maintenance they can become quite useful in roles akin to data analysts, business analysts, and operations managers. They look into data structures, reporting, and process improvement opportunities. They really get to know the organization inside out and look for problems that need solved and the best way to solve them.
It’s a Yes!

- Will you be a real partner for continuous improvement?
- Will you help us develop a reasonable IT budget?
- Will you document our systems and share it with us?
- Will you deal with our IT-related vendors for us?
The answer to every one of these questions is a resounding “Yes!” We strive to align every client’s IT strategy with their business strategy. That strategy includes building a realistic budget for IT hardware and software that takes into account your growth, your goals, and the stability and security of your network. Having thorough documentation is part of having a strong plan for the routine and the unexpected, so we make sure the documentation is always complete, updated, and accessible. And we believe that IT should make your work easier, not harder; so we work with all your IT-related vendors as needed to make sure things keep running smoothly and projects are completed in a timely manner.
Is IT helping you reach your business goals? Our free IT Maturity Evaluation will help you assess how your IT stacks up in four key areas: partnerships, strategy, systems, and settings. Try it out and receive a list of actions you can take to improve your IT. Afterward, you can book a free strategy session to discuss your results with our team.
Take the IT Maturity Assessment

Is your business ready to weather changes, including employee turnover? Find out by taking our IT maturity assessment.
You’ll get personalized action items that you can use to make improvements right away. Plus, you’ll have the opportunity to book a FREE IT strategy session to get even more insights into your IT needs.

Industries
Locations
Waynesboro, VA
Corporate HQ
215 Fifth St.
Waynesboro, VA 22980
Sales: 540-217-6261
Service: 540-885-3129
Accounting: 540-217-6260
Fax: 703-935-2665
Washington D.C.
1126 11th ST. NW
Suite 603
Washington, DC 20001-4366
Sales: 202-888-2770
Service: 866-692-9082
VA DCJS # 11-6604
Locations
Harrisonburg, VA
45 Newman Ave.
Harrisonburg, VA 22801
Sales: 540-569-3465
Service: 866-692-9082
Richmond, VA
3026A W. Cary St.
Richmond, VA 23221
Sales: 804-729-8835
Service: 866-692-9082